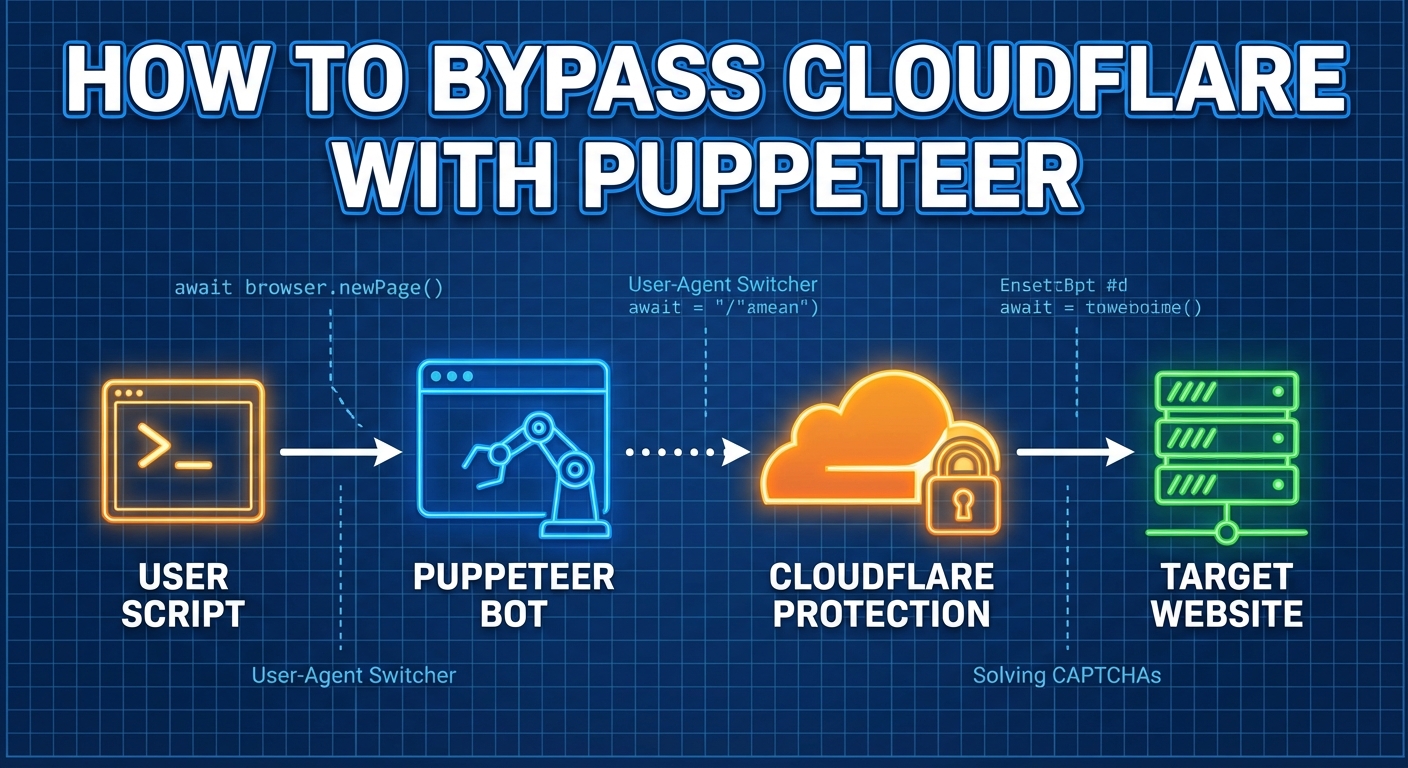
Cloudflare's bot protection blocks default headless Puppeteer scripts almost instantly. However, with a comprehensive strategy, you can successfully bypass Cloudflare challenges and scrape without interruptions. This guide reveals how Cloudflare's multi-layered defense works, why vanilla Puppeteer fails, and provides actionable methods—from stealth plugins to the critical role of 4G/5G mobile proxies. With code examples and honest comparison tables, you'll learn to build reliable, production-grade scrapers that navigate modern anti-bot systems.
Three Essential Pillars for Cloudflare Bypass
For any developer engaged in automated scraping with Puppeteer, encountering Cloudflare is a universal barrier. What starts as a legitimate data collection task can fail when Cloudflare's sophisticated bot detection flags your script, returning an infinite CAPTCHA loop or an outright block.
The core problem lies in Cloudflare's ability to distinguish between a human-operated browser and a headless automation tool. There is no "silver bullet" to fix this. A robust Cloudflare bypass strategy requires a combination of techniques that make your Puppeteer instance indistinguishable from a real user's device across multiple layers.
Effective methods rely on these three core pillars:
- Fingerprint Spoofing: Using libraries to modify Puppeteer's execution environment, hiding automation artifacts (like the
navigator.webdriver flag) to mimic a standard browser. - Network Reputation (Mobile Proxy Routing): Routing requests through highly trusted 4G/5G mobile IP addresses to bypass IP-based bans and maximize your network trust score.
- Behavioral Mimicry: Adjusting browser viewports, avoiding overly linear mouse movements, and executing realistic delays to simulate organic human sessions.
How Cloudflare Detects and Blocks Bots
At the core of Cloudflare's bot detection is a multi-layered system. It combines a JavaScript challenge with advanced fingerprinting, behavioral analysis, and network reputation scoring.
- JavaScript Challenge: A page is served that executes JavaScript to probe for headless-specific properties (e.g.,
navigator.webdriver === true, missing plugins, or specific window.chrome objects). - Browser Fingerprinting: Uses Canvas, WebGL, available fonts, and audio context to generate a consistent browser hash. Headless automation often yields incomplete or uniquely recognizable render results.
- TLS Fingerprinting (JA3/JA4): Analyzes the TLS ClientHello packet's cipher suites. Default Node.js/Puppeteer TLS fingerprints differ heavily from major browsers like Chrome or Firefox.
- Behavioral Analysis: Tracks mouse movement trajectories and scroll patterns. Humans exhibit micro-variations; bots generate mathematically perfect, linear inputs.
- IP Reputation & Trust Score: Cloudflare's global network scores IPs based on historical abuse and ASN types. Datacenter IP ranges carry the lowest reputation, while Mobile IPs carry the highest.
Detection Layer | What Cloudflare Checks | How to Mimic / Bypass |
|---|
JavaScript Environment | navigator.webdriver, Chrome APIs
| Stealth plugins, running in headed mode |
Hardware Fingerprinting | Canvas/WebGL hash, font list | Anti-detect browsers or canvas spoofing |
TLS Fingerprinting | JA3/JA4 hash of ClientHello packet | Use browser-emulating TLS stacks (e.g., curl-impersonate) |
Behavioral Patterns | Mouse movements, click delays | Tools like ghost-cursor, randomized delays |
Network Reputation | Historical abuse reports, ASN type | Use Mobile Proxies (4G/5G CGNAT) |
Running a vanilla Puppeteer script against Cloudflare is the quickest way to get blocked. A basic script that merely launches a browser and requests a protected page triggers defenses instantly.
The Mistake
Using unmodified Puppeteer from a standard hosting provider (like AWS or DigitalOcean). The core issues are Headless Detection, incomplete hardware fingerprints, and worst of all, using Datacenter IPs which Cloudflare treats with extreme suspicion.
const puppeteer = require('puppeteer');(async () => { // Launching in standard headless mode on a Datacenter IP will fail const browser = await puppeteer.launch(); const page = await browser.newPage(); await page.goto('https://target-site.com'); console.log(await page.content()); // Returns Cloudflare challenge page await browser.close();})();
Bypass Methods: From Stealth Plugins to Mobile Proxies
Successfully navigating modern anti-bot systems requires patching both the browser environment and the network layer.
Method 1: The Baseline (Stealth Plugin & Headless Mode)
The puppeteer-extra-plugin-stealth package is the industry standard starting point. Additionally, running Puppeteer in non-headless mode (or the new headless mode) significantly improves success rates.
npm install puppeteer-extra puppeteer-extra-plugin-stealthconst puppeteer = require('puppeteer-extra');puppeteer.use(require('puppeteer-extra-plugin-stealth')());const browser = await puppeteer.launch({ headless: false, // Or 'new' in recent Puppeteer versions args: ['--no-sandbox']});
Reality Check: For low-to-medium security sites, this is often enough. However, on highly protected targets (e.g., sites using aggressive Turnstile rules), the stealth plugin alone will still fail if your IP reputation is poor.
Method 2: Commercial Anti-Detect Browsers
If you need absolute fingerprint perfection, integrating Puppeteer with commercial anti-detect browsers like Kameleo or Multilogin is a powerful approach. These tools shift the burden of spoofing Canvas, WebGL, and TLS away from your script and onto a dedicated engine that perfectly mimics real devices.
Method 3: Solving the Network Layer — Mobile Proxies
Over 80% of scraping blocks originate from poor network reputation. The most robust way to solve the IP layer is by combining your Stealth setup with 4G/5G Mobile Proxies.
Mobile networks use Carrier-Grade NAT (CGNAT), meaning thousands of real smartphone users share a single IP address simultaneously. Cloudflare cannot block a mobile IP without causing massive collateral damage to legitimate users. This grants your script the maximum possible Trust Score on the network level.
Important Nuance: Mobile proxies do not make your script "invisible." They simply remove Cloudflare's strongest filter—IP reputation. You still need DOM stealth and realistic behavior to pass the JS challenges.
Comparing Cloudflare Bypass Solutions
When comparing Cloudflare bypass tools, objective metrics regarding scalability and stealth effectiveness are critical.
Table: Comparison of Cloudflare Bypass Methods
Method | Stealth Effectiveness (1-5) | Scalability | Best Use Case / Core Advantage |
|---|
Stealth Plugin + Datacenter Proxy | 2.5 | High | Low cost, good for lightly protected targets. Fails on IP bans. |
Advanced API Solvers (e.g., FlareSolverr) | 3.5 | High | Automated JS challenge bypassing, doesn't require complex browser management. |
Anti-Detect Browsers (e.g., Kameleo) | 4 | Low to Medium | Perfect hardware fingerprinting, great for multi-accounting. Expensive at scale. |
Stealth Plugin + Mobile Proxies | 4.5 | Medium | Solves the IP reputation problem entirely. The industry standard for production scaling. |
Legal and Ethical Guidelines for Web Scraping
Bypassing security barriers sits in an area that demands professional caution. Circumventing technical barriers for unauthorized access can violate terms of service or laws such as the CFAA. For ethical web scraping:
- Do: Scrape only publicly available data; honor
robots.txt where applicable; use caching and exponential backoff to minimize server load. - Don't: Bypass authentication walls to access private data; hammer servers to cause denial-of-service; scrape PII (Personally Identifiable Information) without consent.
Frequently Asked Questions
Can Puppeteer bypass Cloudflare Turnstile?Turnstile is significantly harder to bypass than older CAPTCHAs because it heavily weighs behavioral metrics and network reputation. A stealth plugin alone usually fails. However, combining a high-trust Mobile Proxy (to pass the IP check) with realistic behavioral scripts (like ghost-cursor for mouse movements) often validates the request seamlessly.How do I effectively rotate proxies in Puppeteer?Pass the proxy server in the launch arguments (--proxy-server=ip:port). For seamless operation without dropping sessions, use mobile proxy providers that handle IP rotation automatically on their backend (e.g., rotating the underlying IP every 5-15 minutes while your gateway port remains constant).Why does Puppeteer get blocked even with the stealth plugin?Stealth plugins only patch DOM and browser properties. If your traffic originates from an AWS data center, Cloudflare's network-level security will block you regardless of how realistic your JS environment looks. The network layer and the execution layer must both be trusted.
Conclusion: Building Resilient Scrapers
Bypassing Cloudflare with Puppeteer requires a balanced, multi-layered approach. Default headless Chrome is highly detectable, making tools like puppeteer-extra-plugin-stealth and running in non-headless mode absolute necessities. However, the true bottleneck in modern scraping is IP reputation. By upgrading your infrastructure to use 4G/5G Mobile Proxies, you eliminate the most common reason for blocks. Implement these layers carefully, operate within ethical boundaries, and you can turn Cloudflare from a hard roadblock into a manageable component of your data pipeline.
Deutsch
Español
Français
Bahasa Indonesia
Polski
Português
Русский
Українська
简体中文